Run Well-Architected assessments across any connected cloud. Screenshots show AWS, but the workflow is provider-agnostic.Documentation Index
Fetch the complete documentation index at: https://docs.cloudthinker.io/llms.txt
Use this file to discover all available pages before exploring further.
The Problem
Well-Architected assessments are valuable but expensive to run. AWS’s own Well-Architected Tool asks hundreds of questions via a manual questionnaire — filling it out accurately requires an engineer who knows the environment deeply, takes 2–4 days, and produces a point-in-time report that’s stale the moment your infrastructure changes. Third-party assessments from cloud consultants cost 50,000 and happen once or twice a year. The result: most teams either skip assessments entirely or run them only when an audit requires it — meaning architectural risks compound undetected for months.How Existing Tools Compare
| Tool | What It Does | What’s Missing |
|---|---|---|
| AWS Well-Architected Tool | Manual questionnaire for 6 pillars | Completely manual — requires engineer time to fill out; no automated discovery of actual infrastructure state |
| AWS Trusted Advisor | Automated checks against ~50 best practices | Limited scope, no framework mapping, no multi-cloud, no AI analysis |
| Cloud consultants | Expert-led assessments | Expensive ($15K–50K), infrequent, findings go stale before remediation completes |
| Security CSPM tools | Security pillar only | Cover one pillar (security), not cost, performance, reliability, or operational excellence |
What Makes This Different
- Automated, not questionnaire-based: agents read your actual infrastructure configuration — no manual Q&A required
- All 6 pillars: Cost Optimization, Security, Reliability, Performance Efficiency, Operational Excellence, and Sustainability in one run
- Runs on your discovered resources: scoped to the exact resources you care about — production only, specific services, specific regions
- Actionable findings: every finding includes effort, risk, dollar savings estimate, and step-by-step remediation — not just “this is a gap”
- Repeatable: run monthly or after major infrastructure changes — not once a year
Assessments are available on the Advanced plan.
Prerequisites
- A cloud connection with the permissions your agents need to assess resources.
- Resources already discovered in CloudThinker; assessments only evaluate discovered resources.
- Optional: tag or resource filters ready if you want to scope the run.
Assessments are limited to discovered resources. CloudKeepers automations
still operate across any resources you permit in your cloud connection.
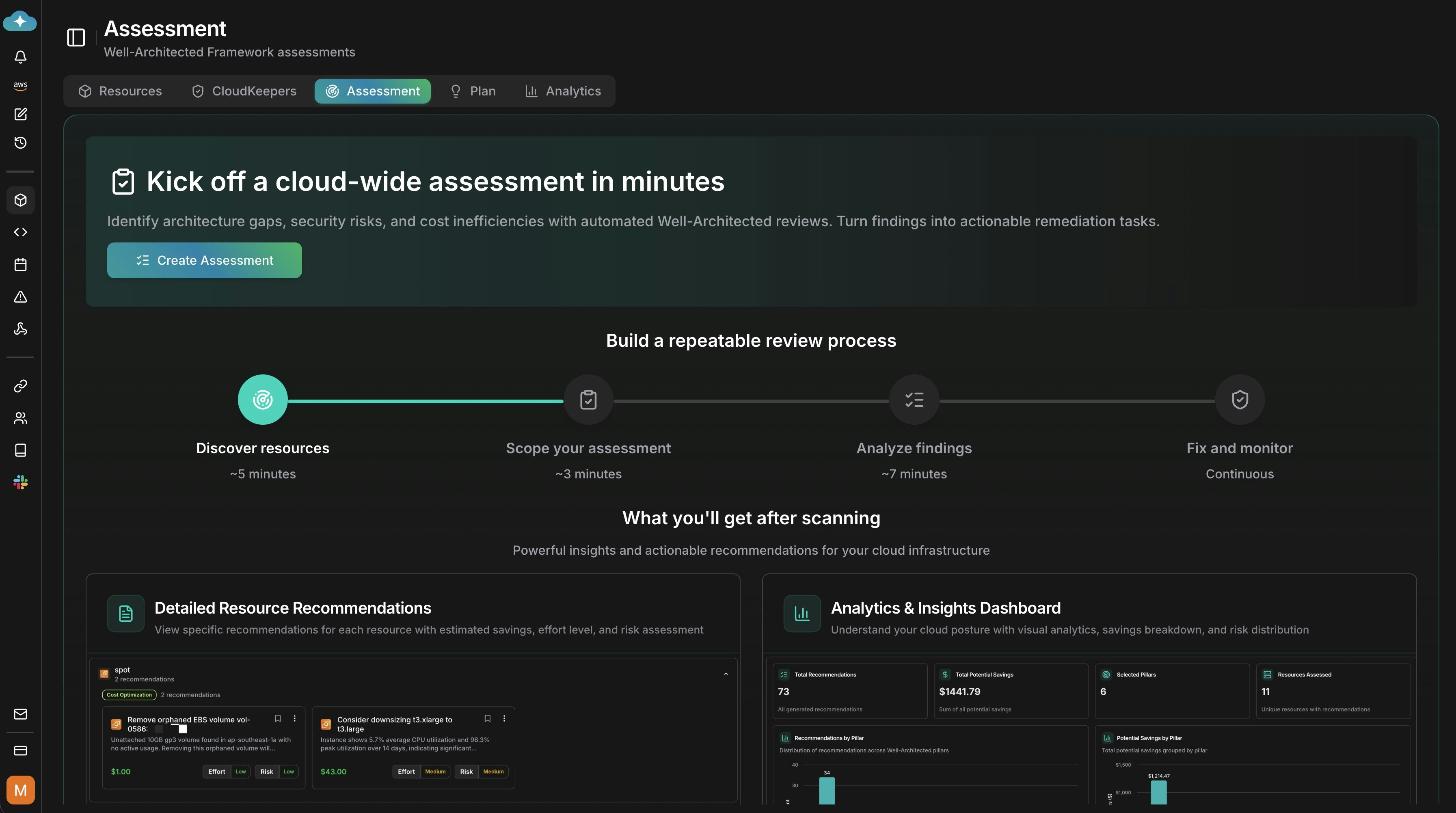
Step-by-Step Guide
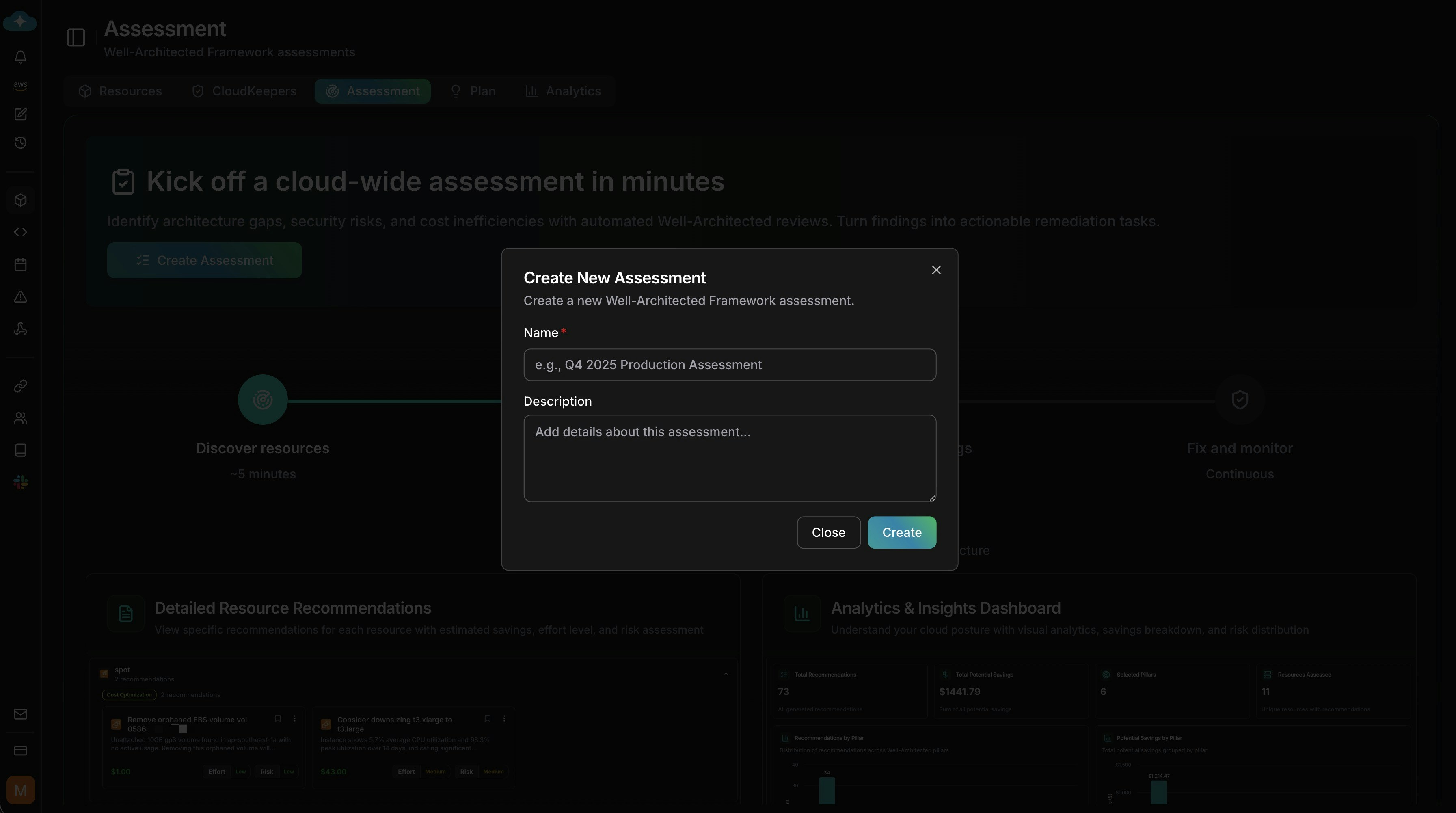
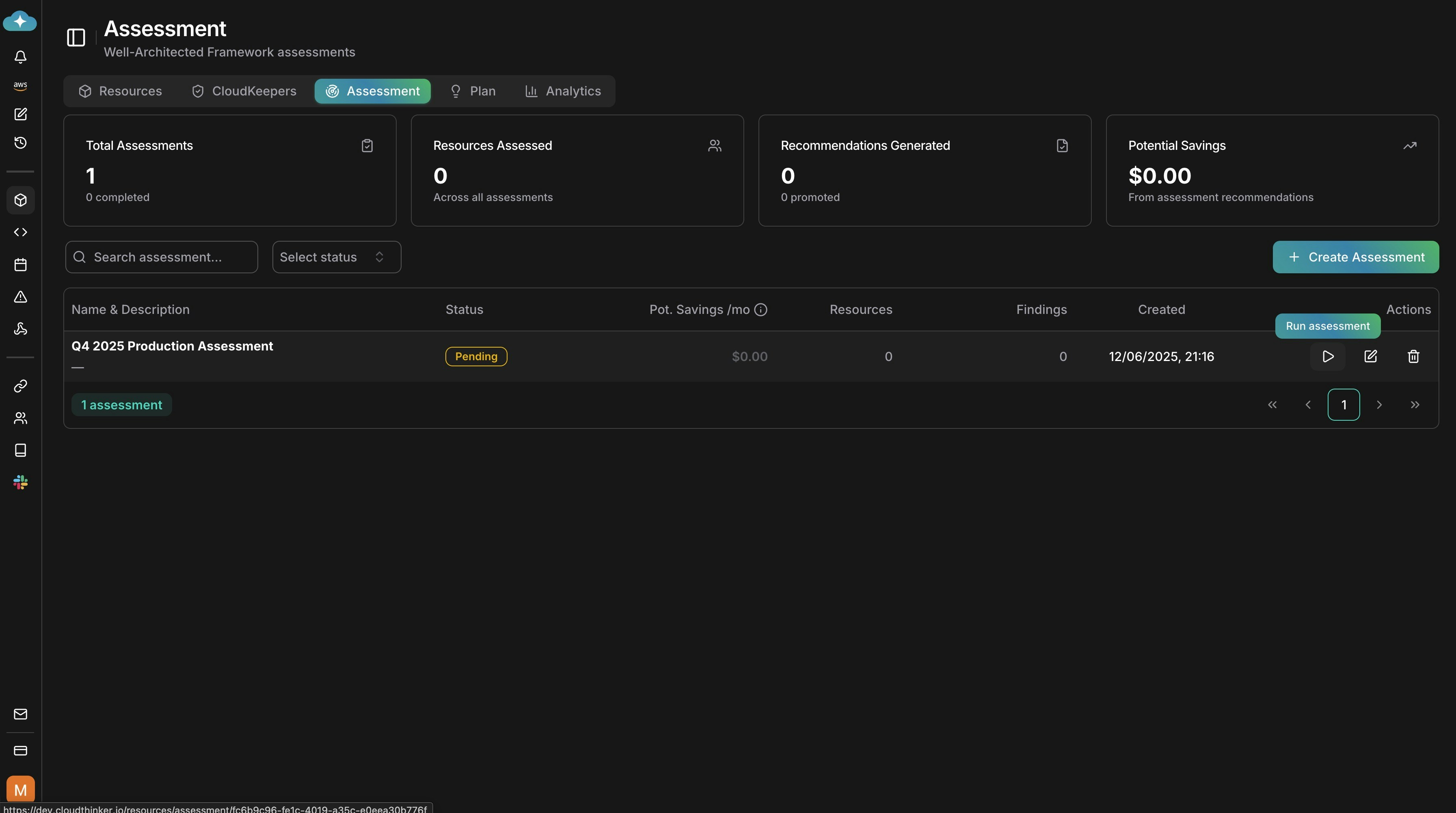
Step 1: Create an Assessment
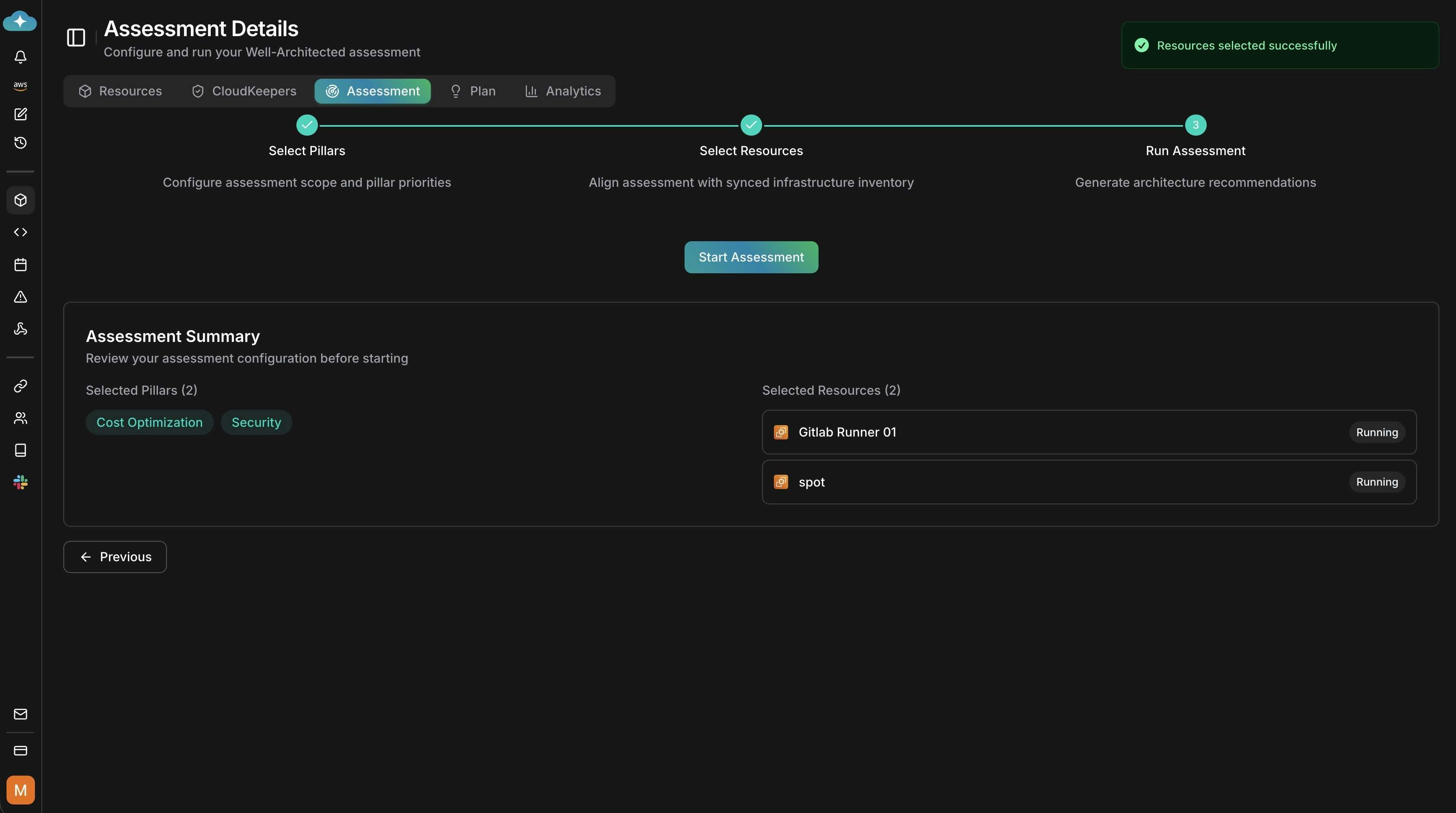
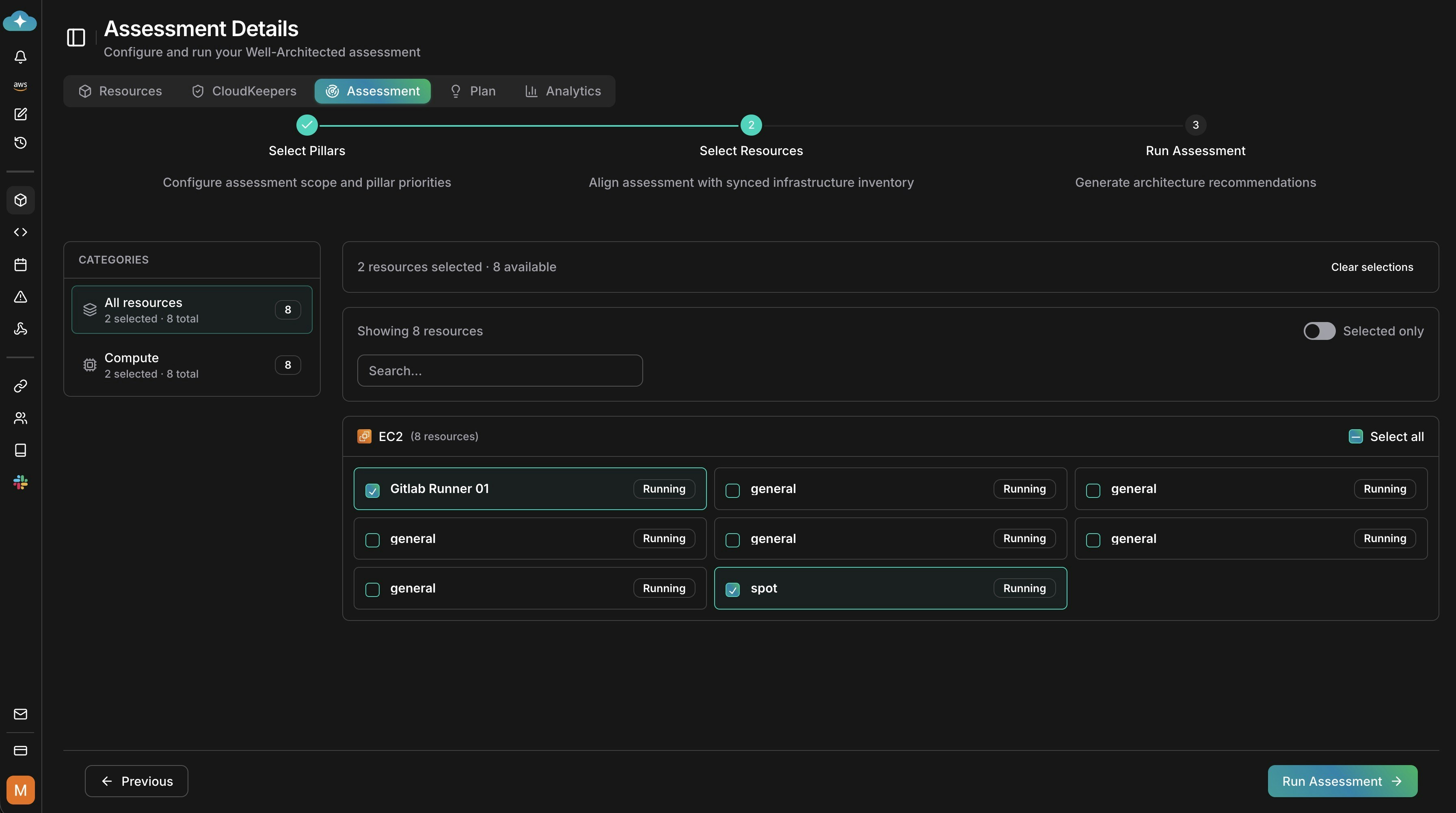
Step 2: Configure the Assessment
Select Well-Architected pillars
Pick the pillars to evaluate (e.g., Cost Optimization, Security, Reliability, Performance Efficiency, Operational Excellence, Sustainability).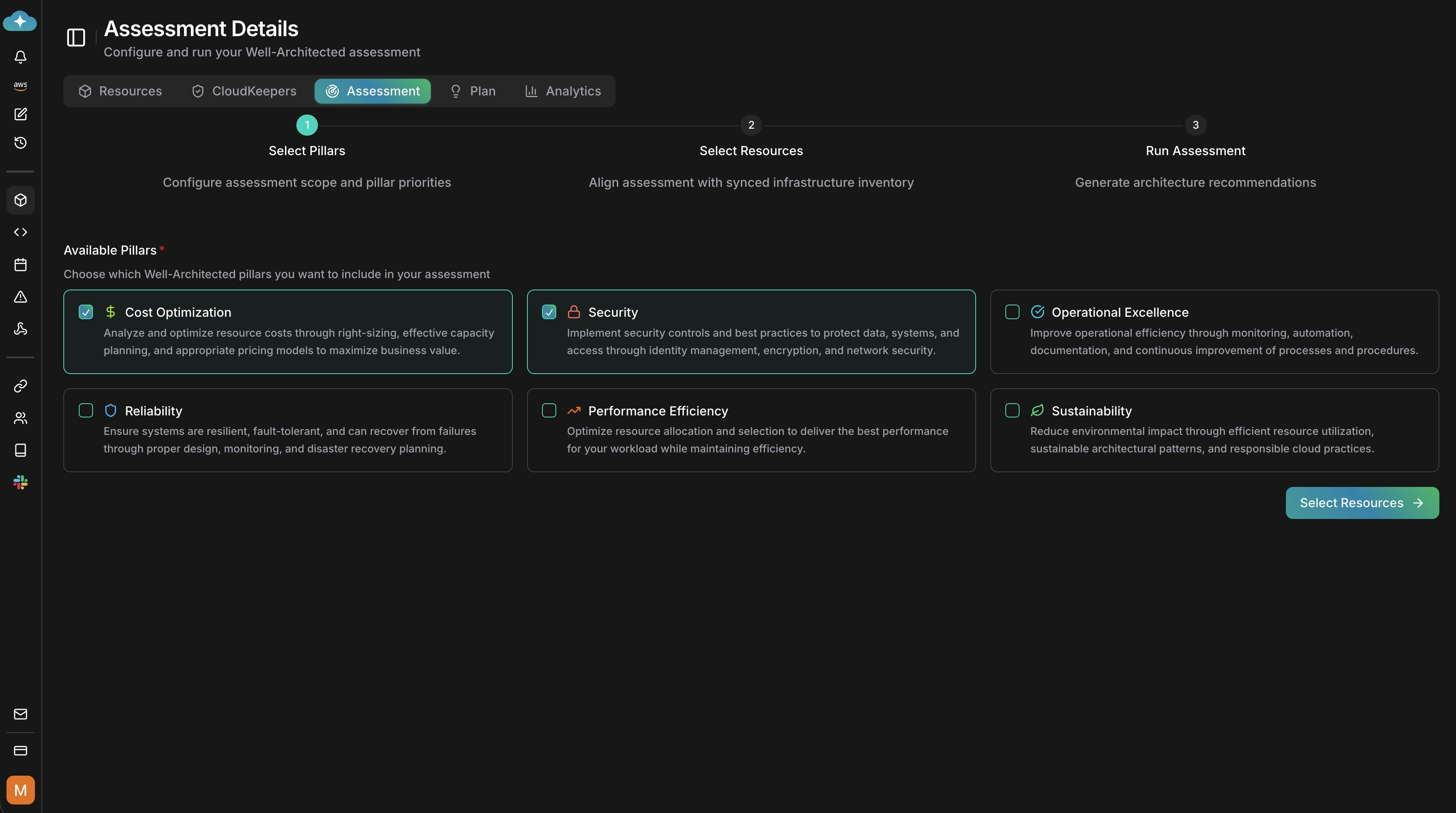
Select resources to assess
Choose the discovered resources you want to include. You can scope to categories or specific resources. Only discovered resources are assessable.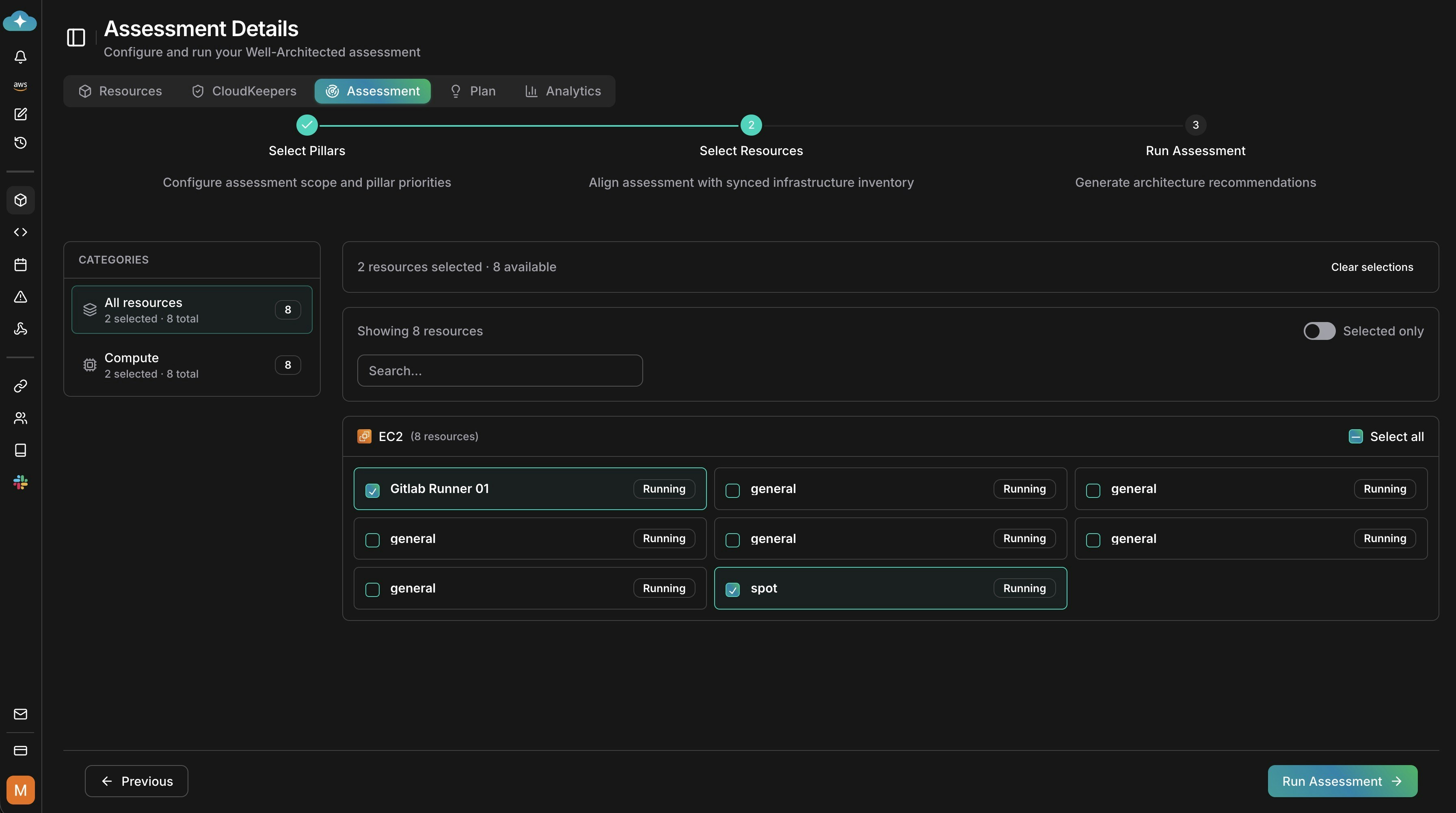
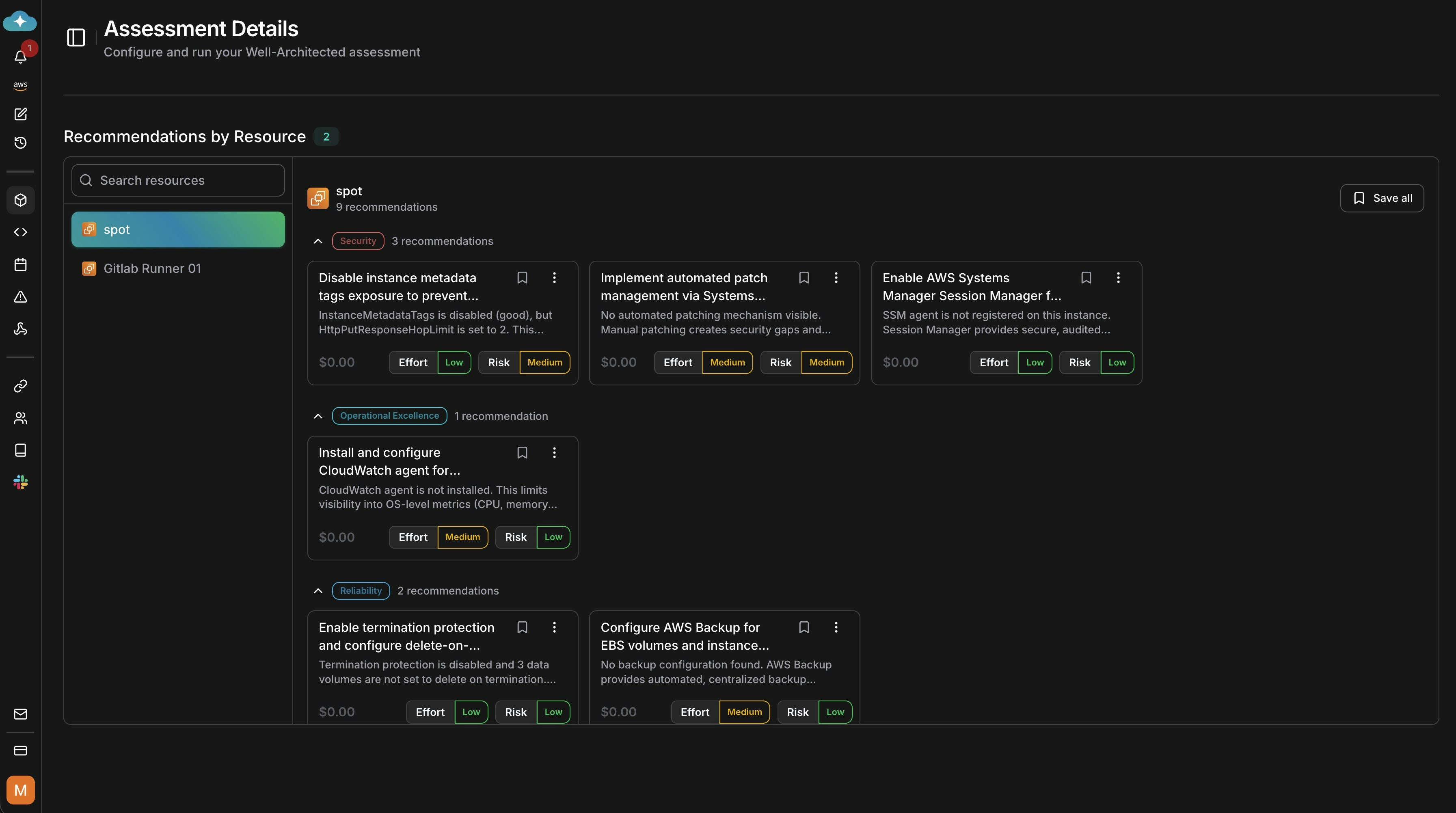
Step 3: Review Results and Take Action
View analytics and findings
After the run, review analytics for findings by pillar, potential savings, and scope.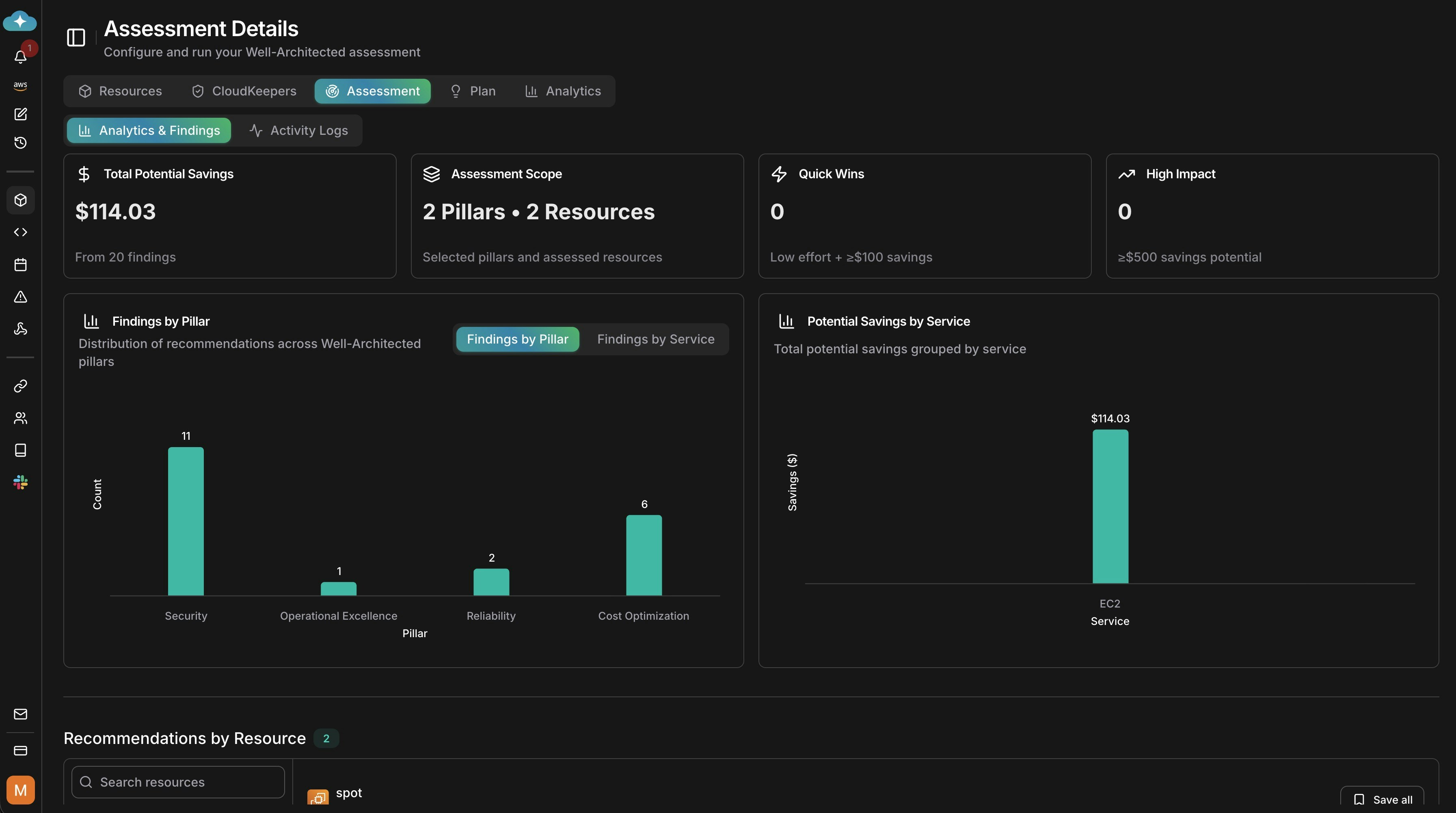
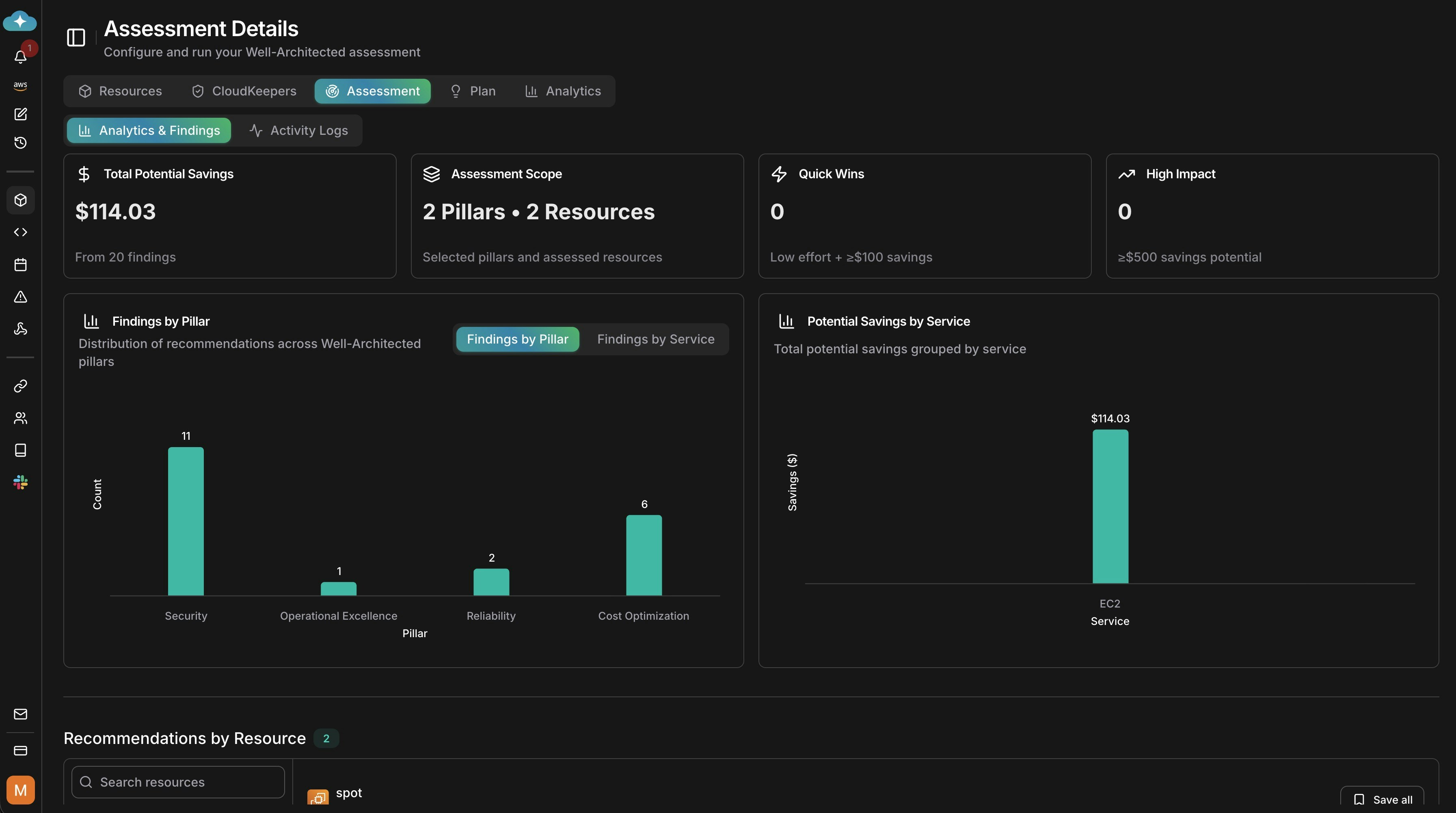
Drill into recommendations
Expand recommendations by resource to see effort, risk, and remediation details you can action.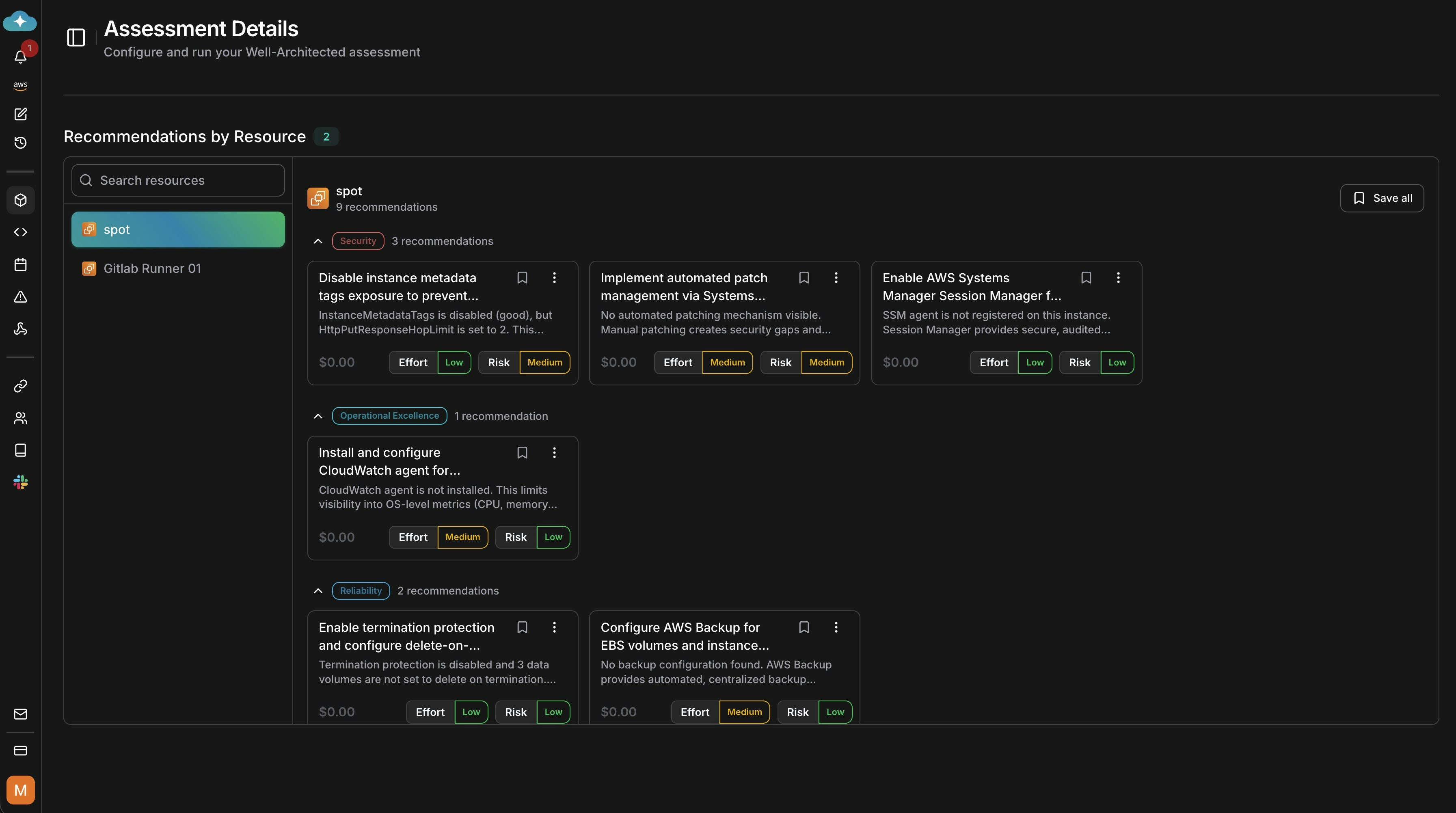
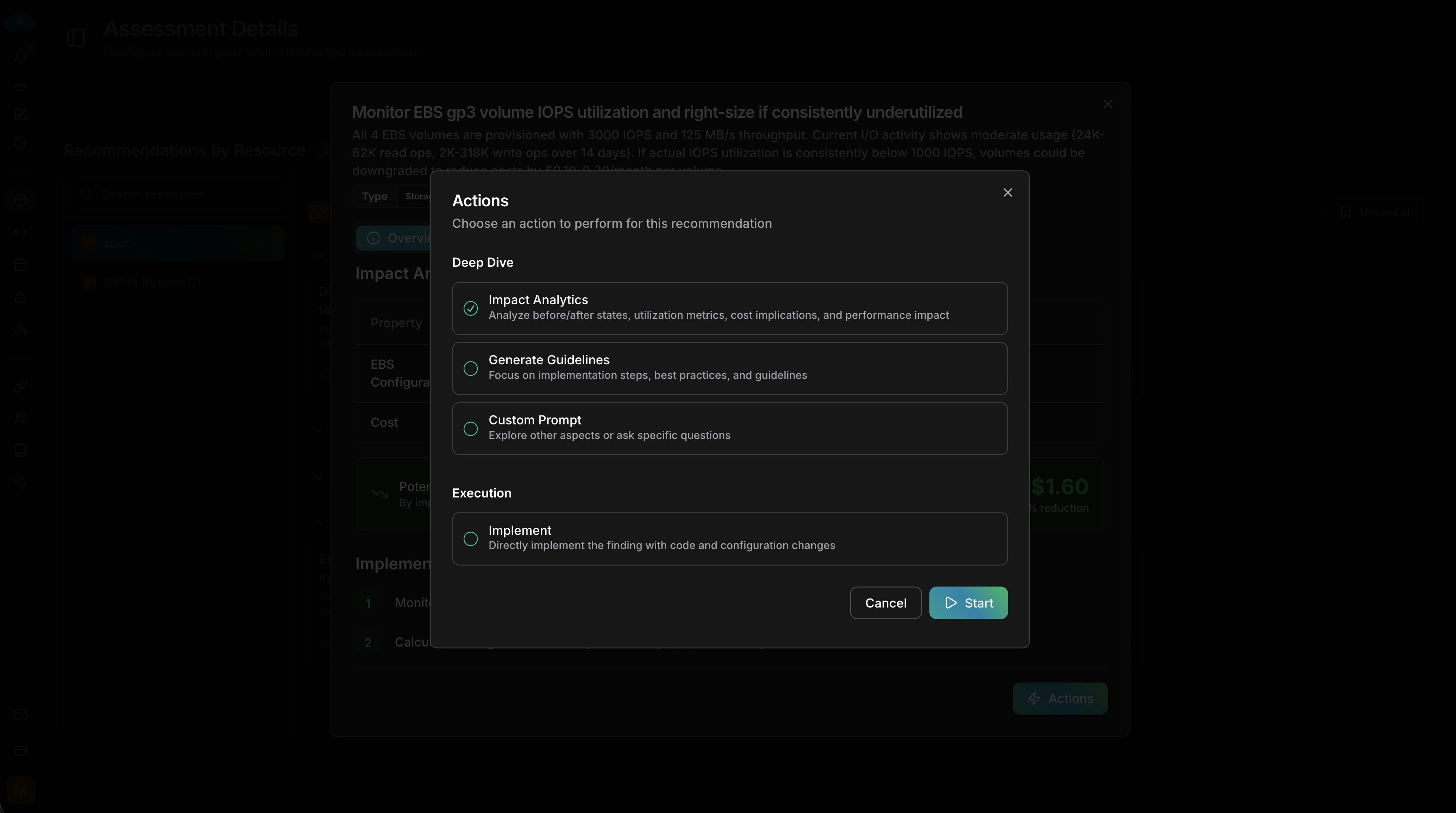
Open recommendation details
Click a recommendation to view impact analysis, savings, and implementation guidelines.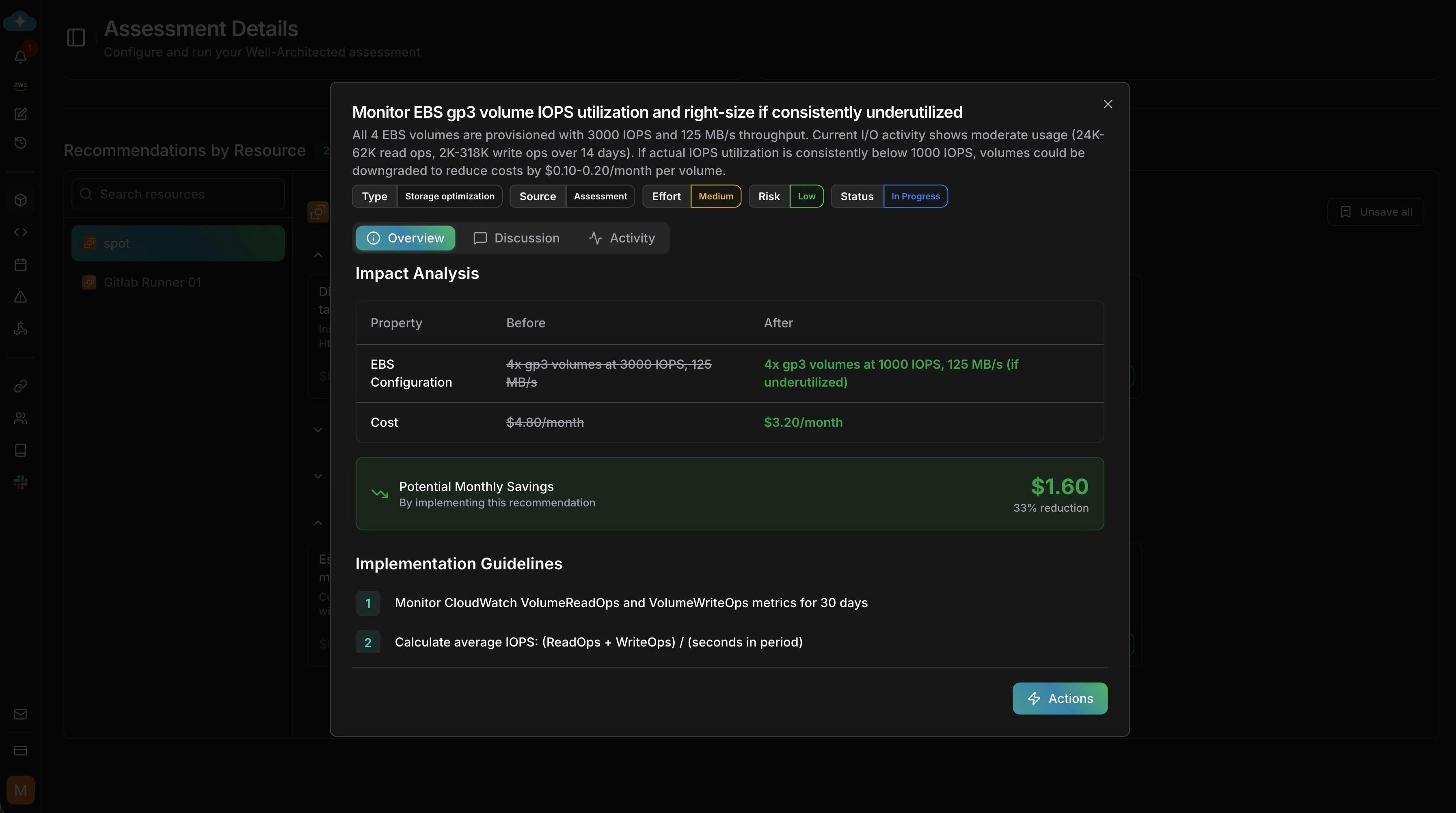
Recommendations are drafted by default—save them to make them appear on the
Plan page.
What’s Next
Plan
Save assessment findings to Plan to track implementation and ROI
CloudKeepers
Set up daily guardrails to maintain the standards your assessment identified
Resources
Discover additional resources to include in your next assessment run
Cost Optimization
Deep-dive into cost findings from the Cost Optimization pillar